A new report that looks at the big picture pegs the worldwide haul from cybercrime at 1.5 trillion dollars. That’s not just criminal business, it’s an entire criminal economy, say the authors of the report, “Into The Web Of Profit.” So what’s this about secret sauce? Well, you’ll have to read on for that…
What do you know? Crime DOES Pay! 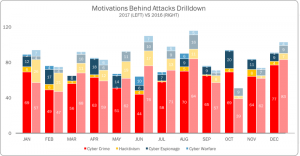
The cybercrime report was researched at the University of Surrey (UK) and commissioned (paid for) by Bromium, a startup security software firm that must have a lot of venture capital behind it.
The security software market has dozens of entrenched players, many of which are household names at least among computer-housing households. Think Symantec, McAfee, Avast, AVG, Kaspersky, Bitdefender, and all of the others I have tested over the years. To gain a profitable market share, Bromium will need some “secret sauce” that nobody else has and which sounds terribly sexy to its prospective users.
Sure enough, Bromium has it: “virtualization-based security” is what they’re selling, and it doesn’t come cheap; I know because no price is to be found anywhere, just “contact us for a demo” buttons on every page of Bromium’s site. Here is the company’s own explanation of its secret sauce:
“The Bromium Secure Platform protects you from threats by isolating user tasks, such as email attachments, links, and downloads, inside protected micro-virtual machines — a separate VM for each task. If malware is delivered, it can’t escape. Users can click with confidence.” (Sounds more like “reckless abandon” to me.)
Bromium’s tech was tested by NSS Labs and got a perfect score in defeating all malware and even expert human attempts at penetration. So you might be wondering if there’s a free version of Bromium for personal use. Fuggedaboutit… Bromium’s solution requires a specially equipped computer connected to a corporate network. Their product is aimed at companies, not consumers. But the cybercrime report that Bromium bought is useful and free.
Dr. Michael McGuire is a Senior Lecturer in Criminology at Surrey University, England. He spent nearly a year figuring out where the money goes after a ransom is paid or intellectual property is stolen. Let’s look at some the highlights of his report.
First, the cybercrime economy moves very fast! There are no hours-long lunches at Luigi’s where plots are discussed
obliquely; these criminals use encrypted, short-lived channels to make deals, swap data, commit crimes, and move on before Don Corleone puts a spoon to his spumoni.
Second, the real world of crime is blending into the cybercrime world. According to the report, “Companies and nation states now make money from it (the cybercrime world), acquire data and competitive advantages from it, and use it as a tool for strategy, global advancement and social control.”
Today’s Cybercrime is Carefully Planned and Executed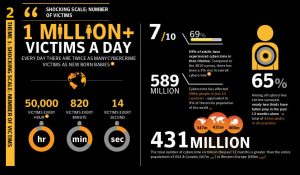
Gone are the days when “hacking” was just a prank, or a way to show off your skills to your circle of hacker pals. Today’s cybercriminal is in it for the money, sonny, and not for the laughs. There are no more “random attacks,” it’s all very carefully planned and executed.
The report contends that cybercrime “has now become a kind of mirror image of contemporary capitalism – reproducing disruptive business models popularised by the likes of Amazon and Uber.” The report lists a number of ways in which the cybercrime economy has copied the wealth-generating techniques developed by the legitimate information economy; here are just a few of them:
- A dizzying range of methods and mechanisms for generating revenues, often at industrial scales.
- Digitally specific currencies and currency exchange tools. (Somebody must be using those hundreds of Bitcoin imitators.)
- A range of specialised economic agents, such as producers, suppliers, service providers and consumers.
- The extraction and exchange of data as the key raw material and object of value for illicit trading (this trade now occurs across many dimensions and no longer simply involves buying or selling data from stolen credit or debit cards, but newer data forms that possess value – such as hotel loyalty points, ‘likes’ on Facebook, account login details and even soft drink formulas or government-developed hacking tools).
- Dedicated production zones and centres of income generation – whether these be troll factories in Russia, the Hackerville fraud villages in Romania, or mass marketing scam centres in West Africa.
- Specialised tool supply, technical support and provision of skills and expertise.
- Professionalisation and the development of career structures – this includes training, CVs, personal recommendations and references.
Okay, let’s stop at the thought of hackers with resumes and references, marching (or video-calling, more likely) into the HQ of a Russian troll factory to apply for a job. That’s enough to freeze my brain.
Following the Money
The scariest headline-grabbing cybercrimes are barely registering on the global economy’s meter. Ransomware and “cyber-crime-as-a-service” each contributes less than 1 percent to the cybercrime economy. None the less, the FBI estimates worldwide revenues from ransomware were about $1 billion in 2017.
Also, cryptocurrencies such as Bitcoin may not play as large a role in cybercrime as the popular press has suggested. Only about 4 percent of laundered money – proceeds of crime that have been processed through enough legitimate online payment systems to appear “clean” or at least “not guilty” – is held in cryptocurrencies. The rest has found its way into more legitimate currencies and bank accounts, or is even used to buy tangible, untraceable commodities like gold or oil directly with cryptocurrencies.
And surprisingly, trade in stolen identities is not one of the biggest contributors to the cybercrime economy. In fact, such trade accounts for “only” $160 billion of the $15,000 billion cybercrime economy.
Trade in illegal drugs and other physical contraband accounts for $860 billion. Thefts and sales of “trade secrets,” such as soft drink recipes, and other intellectual property score $500 billion, and “data trading” brings in another $160 billion. “Data trading” is what happens after you lose your wallet, but on a much larger (digital) scale.
I have to wonder, given the labyrinthine world of cybercrime, how much of the digital iceberg Dr. McGuire was able to discover. The fact that he lives to tell may indicate that he’s only scratched the surface. Still, the report makes fascinating reading if you are interested in either crime or how cybercrime economies form, grow more complex, and eventually become dark shadows of the economies upon which they prey.
Have a great week
ZI Staff